كيف يمكن لنقطة بيع آمنة ضمان معاملات مالية آمنة
التقنيات الأمنية الأساسية في أنظمة نقطة البيع الآمنة
التشفير من النهاية إلى النهاية لحماية البيانات
تُعد التشفير من طرف إلى طرف (E2EE) دورًا حيويًا في الحفاظ على سلامة معلومات العملاء داخل أنظمة نقاط البيع الآمنة. عندما يقوم شخص ما بتمرير بطاقته الائتمانية عند نقطة الدفع، تقوم هذه التكنولوجيا بتحويل جميع تلك الأرقام إلى بيانات غير قابلة للقراءة من قبل أي شخص باستثناء معالج الدفع نفسه. هذا يعني أنه لا يمكن للمخترقين التجسس على البيانات أثناء انتقالها عبر الشبكات. تُعد تسريبات البيانات ضربًا قويًا للأعمال التجارية في الوقت الحالي. تُظهر الإحصائيات أن حوالي 60 بالمئة من الشركات الصغيرة تُغلق أبوابها بالفعل بعد التعرض لهجوم سيبراني وفقًا لأبحاث حديثة حول أمن أنظمة نقاط البيع من شهر مايو 2024. كيف يعمل E2EE؟ في الواقع، يقوم هذا النظام بتحويل البيانات العادية إلى بيانات غير مفهومة باستخدام صيغ رياضية خاصة تُعرف باسم خوارزميات التشفير. ويظل هذا التشفير ساريًا من اللحظة التي تُجمع فيها البيانات وحتى وصولها إلى وجهتها النهائية.
تكنولوجيا شريحة EMV: ما وراء الشريط المغناطيسي
إن تقنية شريحة EMV التي طورتها شركات Europay وMasterCard وVisa تقلل بشكل حقيقي من الاحتيال في حالات استخدام البطاقة بشكل مادي، وذلك لأنها تُنشئ أكوادًا مختلفة لكل عملية شراء عند استخدام البطاقة. وبعد أن بدأ اعتماد هذه التكنولوجيا على نطاق واسع في الولايات المتحدة، انخفض الاحتيال المرتبط باستخدام البطاقات ماديًا بنسبة 76% تقريبًا. وهذا انخفاض كبير مقارنة بالماضي حينما كان من السهل جدًا تكرار البيانات من الشريط المغناطيسي القديم. الانتقال من هذه الأشرطة الضعيفة إلى الشرائح الإلكترونية يجعل الأمور أكثر أمانًا بشكل كبير، إذ لم تعد البطاقات المزيفة فعالة كما كانت من قبل. أما بالنسبة للشركات، فإن مواكبة معايير EMV ليست مجرد ممارسة جيدة، بل هي ضرورية إذا أرادت حماية أموال العملاء وبناء علاقات ثقة دائمة.
الرمزنة: استبدال البيانات الحساسة
يبرز الترميز كأحد أهم إجراءات الأمان في أنظمة نقاط البيع اليوم. يعمل هذا الترميز عن طريق استبدال أرقام بطاقات الائتمان الحقيقية برموز عشوائية. عند حدوث ذلك، لا تُحفظ المعلومات الحساسة في أي مكان في النظام نفسه. حتى لو تمكن أحدهم من سرقة هذه الرموز، فلن تكون ذات قيمة للمخترقين الذين يحاولون ارتكاب عمليات احتيال. تُظهر أبحاث القطاع أنه عندما تطبق الشركات الترميز، فإنها توفر حماية أفضل لبيانات عملائها، وتُسهّل أيضًا تلبية معايير PCI المعقدة (للمزيد من التفاصيل، يُرجى الاطلاع على "أمان نقاط البيع: 11 أفضل ممارسة لإدارة أعمالك بدقة في عام 2024"). تُعزز الشركات التي تتبنى هذا النهج وضعها الأمني العام، وتمنح المتسوقين راحة البال لعلمهم بأن معاملاتهم تُدار بأمان.
الامتثال والمعايير لأمان نقطة البيع
متطلبات PCI DSS للمعاملات الآمنة
يؤدي معيار أمان بيانات صناعة بطاقات الدفع، المعروف اختصارًا بـ PCI DSS، دورًا حيويًا في ضمان سلامة المدفوعات عندما يستخدم العملاء أنظمة نقاط البيع. ببساطة، هو مجموعة من القواعد والإرشادات التي تهدف إلى حماية المعلومات الحساسة الخاصة ببطاقات الائتمان طوال عملية المعاملة. تشير الأبحاث إلى أمر هام هنا أيضًا - الشركات التي تلتزم بهذه المعايير تتجنب حدوث اختراقات بيانات بنسبة 48٪ أكثر من تلك التي لا تلتزم. هذا النوع من الحماية له أهمية كبيرة في البيئة الرقمية الحالية حيث تتطور التهديدات الإلكترونية باستمرار. يحتاج التجار الراغبون في تنظيم أوضاعهم فيما يتعلق بالامتثال لمعايير PCI إلى الوفاء بمتطلبات متعددة تشمل على سبيل المثال لا الحصر إجراءات أمن الشبكات، والقيام بمسح دوري للثغرات الأمنية، ووضع برامج تدريبية مناسبة للموظفين.
- صيانة الشبكة الآمنة : استخدم جدران الحماية وتقنيات أمان أخرى لحماية الشبكات من الوصول غير المصرح به.
- حماية بيانات حامل البطاقة : شفر نقل بيانات حامل البطاقة عبر الشبكات العامة المفتوحة لضمان سلامة البيانات.
- تنفيذ التحكم في الوصول : قيد وصول البيانات بناءً على الحاجة الوظيفية؛ واستخدام هويات فريدة والتحقق متعدد العوامل.
- مراقبة واختبار مستمر : راقب الشبكات بانتظام واختبر أنظمة الأمان لاكتشاف الثغرات المحتملة.
- سياسة أمان المعلومات : إنشاء وصيانة سياسة شاملة لمعالجة أمن البيانات عبر المنظمة.
تؤدي هذه الإرشادات ليس فقط إلى حماية الشركات من الخسائر المالية، ولكنها أيضًا تحمي المصداقية السمعة من خلال إثبات التزامها بمعالجة الدفع الآمن.
دور SSL/TLS في بوابات الدفع الآمن
تساعد بروتوكولات SSL و TLS في حماية البيانات أثناء انتقالها بين أنظمة نقاط البيع والخوادم الخلفية. كما أنها تمنع المتسللين من اعتراض الاتصالات أثناء نقلها، مما يحافظ على أمان قنوات المعاملات. وعندما تظل البيانات سرية وسليمة أثناء النقل، يشعر العملاء بشكل طبيعي بأن التعامل الرقمي أكثر أمانًا. كما تعطي محركات البحث أولوية للمواقع التي تستخدم أمان SSL، مما يعني ترتيبًا أفضل في صفحات النتائج وزيادة في حركة المرور على المواقع التجارية. تحتاج بوابات الدفع إلى حماية SSL/TLS للعمل بشكل صحيح، مما يجعل هذه البروتوكولات ضرورية لأكثر من مجرد تلبية احتياجات التشفير الأساسية. فهي تخلق تجربة تسوق أكثر أمانًا بشكل عام. إن الشركات التي تطبق ممارسات تشفير قوية من خلال SSL/TLS لا تحمي نفسها فحسب، بل توفر أيضًا للعملاء ثقة بأن معلوماتهم الشخصية والمالية محمية ضد التهديدات الإلكترونية.
بنية أجهزة نقاط البيع الآمنة
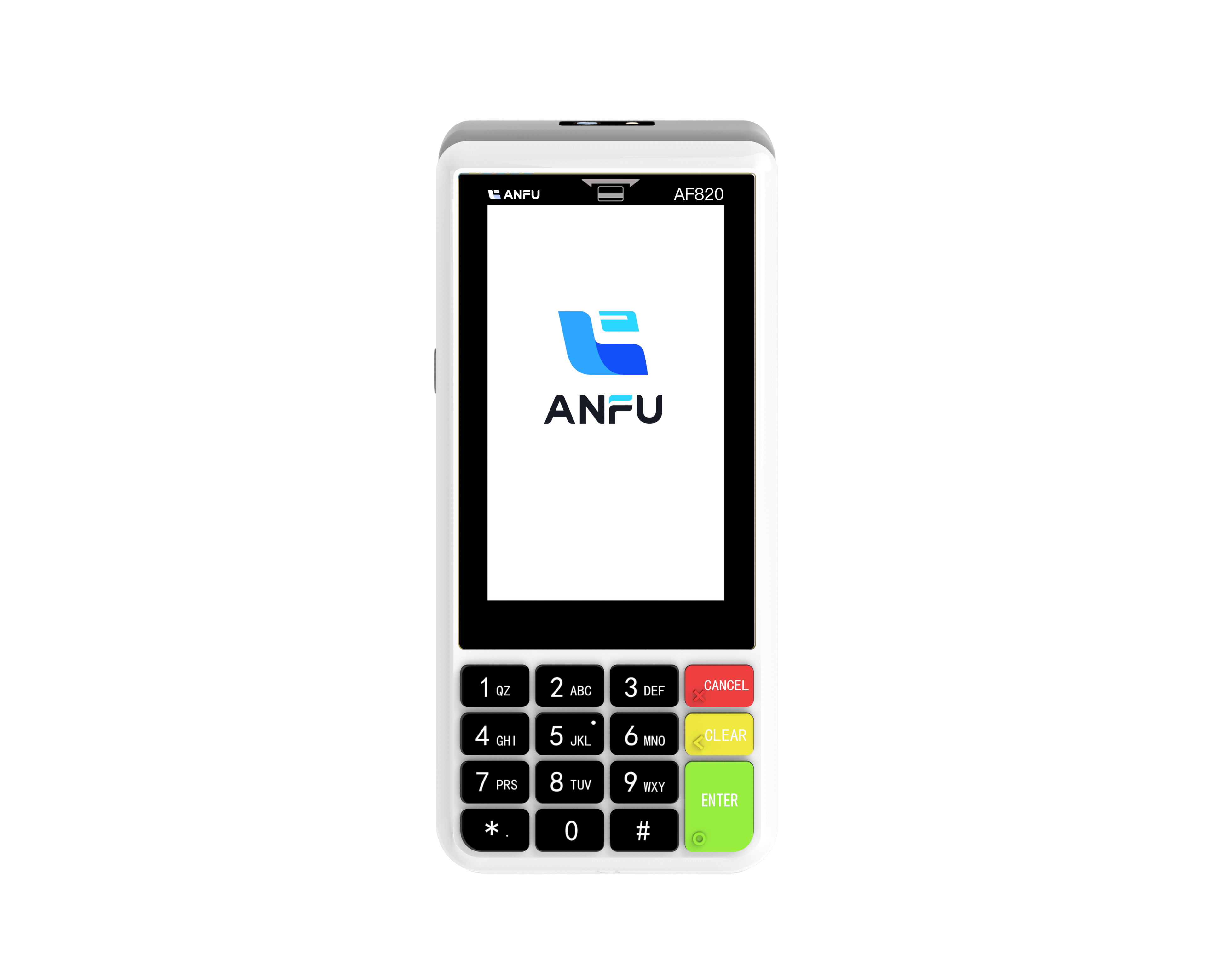
أجهزة نقاط البيع الذكية بنظام أندرويد لمتاجر التجزئة الحديثة
أنظمة نقاط البيع المدعومة بأندرويد تُغير طريقة عمل المتاجر اليوم. تأتي هذه الأنظمة بشاشات سهلة الاستخدام، ومع مجموعة كبيرة من التطبيقات التي يمكن تثبيتها، وتعمل بسلاسة مع طرق دفع مختلفة، مما يُحسّن تجربة التسوق للعملاء. يحب تجار التجزئة هذه الأجهزة لأن منصّة أندرويد تتيح لهم تعديل عمليات أعمالهم بسهولة نسبيًا. علاوة على ذلك، تكون التكاليف التشغيلية عادةً أقل مقارنة بالأنظمة القديمة. يتوقع محللو السوق مستقبلًا واعدًا لمحطات نقاط البيع الذكية، حيث يُفضّل المزيد من الناس الدفع أثناء التنقّل بدلًا من الانتظار في الطوابير أمام أجهزة الاستقبال التقليدية. ومن المنطقي أن تزداد شعبية هذه الأجهزة القائمة على أندرويد عند النظر إلى ما يحدث يوميًا في المتاجر الواقعية، حيث يكون الدفع السريع والمأمون أمرًا بالغ الأهمية خلال فترات الذروة.
فوائد أجهزة الـ POS المحمولة المصغرة
يحب العملاء أجهزة نقاط البيع المحمولة والصغيرة لأنها تتيح للمتاجر معالجة المدفوعات في نفس المكان الذي يقف فيه المتسوقون، مما يجعل الأمور أسهل وأكثر سعادة للجميع. يشهد البائعون الذين يعتمدون هذه الأجهزة الصغيرة تسارع عمليات الدفع في جميع المجالات، مما يعني أن الأشخاص يقضون وقتًا أقل في الانتظار في الطوابير وأكثر وقتًا في التسوق فعليًا. وبحسب أحدث الدراسات السوقية، يفضل حوالي سبعة من كل عشرة عملاء التسوق في أماكن توفر خيارات الدفع أثناء التنقل. كما تحقق هذه الأنظمة الصغيرة لتسجيل المبيعات نتائج رائعة في تتبع أرقام المبيعات أيضًا، وتجعل العمليات اليومية تعمل بسلاسة أكبر خلف الكواليس. وبالإضافة إلى ذلك، عندما يستطيع الموظفون التفاعل مع العملاء وجهاً لوجه أثناء المعاملات بدلًا من الاختباء خلف الطاولات، فإنهم يخلقون تلك الروابط الشخصية القيّمة التي تجعل المتسوقين يعودون مرارًا وتكرارًا.
استراتيجيات وقائية لمكافحة الاحتيال
المراقبة الفورية وإشعارات النشاط المشبوه
إن توفر أدوات المراقبة في الوقت الفعلي يُحدث فرقاً كبيراً عندما يتعلق الأمر باكتشاف أنماط الاحتيال والحصول على التنبيهات بسرعة كافية لإيقاف المشاكل قبل أن تتفاقم. تقوم هذه الأنظمة بمراقبة بيانات المعاملات باستمرار، مما يمكّن الشركات من اكتشاف أي شيء غير طبيعي والتحرك فوراً قبل أن يُحدث المُجرمون ضرراً. الأرقام الخاصة بالقطاع تدعم هذا الأمر بشكل واضح أيضاً، إذ تشير إلى أن أصحاب الأعمال الذين قاموا بإضافة مراقبة في الوقت الفعلي يسجلون نحو ثلث عدد محاولات الاحتيال مقارنة بالأخرى، مما يُظهر كفاءة هذه الأدوات في الحفاظ على الأمان. وعند دمجها مع أنظمة نقاط البيع الحالية، تصبح عملية اكتشاف الاحتيال أكثر فعالية. وعند توصيل الأنظمة المختلفة للعمل معاً بسلاسة، فإن ذلك يمنح الشركات تغطية أكثر شمولاً ضد محاولات السرقة والتسريبات دون عناء.
التحكم في الوصول بناءً على الأدوار لأمن الموظفين
عندما تطبق الشركات تحكم الوصول القائم على الأدوار (RBAC)، فإنها بفعالية تحد من الأشخاص القادرين على رؤية المعلومات. تظل البيانات الحساسة محمية من جميع الموظفين باستثناء من يحتاجونها فعليًا لأداء مهام وظيفتهم. الشيء المثير للاهتمام هو الطريقة التي يقلل بها هذا النظام من المشكلات الناتجة عن المستخدمين الداخليين. تُظهر أمثلة واقعية أن الشركات التي تستخدم RBAC تميل إلى امتلاك عدد أقل بكثير من حالات سوء استخدام البيانات من قبل الموظفين، وذلك لأن الوصول مرتبط مباشرةً بالدور الوظيفي للشخص وما يحتاجه فعليًا لأداء عمله. بالنسبة لأي شخص يسعى لتطبيق RBAC بشكل صحيح، هناك بعض الأمور الأساسية التي يجب تذكرها. تُعد المراجعات الدورية لمن يمتلك حقوق الوصول، وضمان فهم الموظفين لأهمية هذه القيود، أجزاءً أساسية للحفاظ على كفاءة النظام. تنتهي الشركات التي تلتزم بمراجعات مستمرة وتحرص على تعليم موظفيها باستمرار حول أمن المعلومات إلى احتمالات أقل بكثير لحدوث مشكلات داخلية، مع الحفاظ على تحكم جيد في أنظمتها لنقاط البيع.
أفضل الممارسات لتعزيز أمان نقاط البيع
تحديث البرامج وإدارة التعديلات بانتظام
من المهم حقًا تحديث برامج نقاط البيع بانتظام إذا أرادت الشركات أن تظل محمية من الثغرات الأمنية والتهديدات الإلكترونية. تُظهر الإحصائيات أمرًا مذهلاً في الواقع: حوالي 90 بالمئة من جميع محاولات القرصنة الناجحة تستهدف ضعفًا كان معروفًا بالفعل ويمكن إصلاحه من خلال تحديثات بسيطة. هذا يُظهر فقط مدى أهمية التحديثات المنتظمة حقًا. وسيلة ذكية لتنفيذ هذه التحديثات هي جدولتها في أوقات لا تكون فيها المتاجر مشغولة، ربما في أوقات متأخرة من الليل أو في الصباح الباكر، حتى لا يتم إزعاج العملاء. يجب على الشركات التركيز أولًا على إصلاح تلك الثغرات التي تم تصنيفها على أنها عالية الخطورة وفقًا لتقييمات الأمان، حيث أنها تمثل الخطر الأكبر. عندما تضع الشركات هذا النوع من الروتين الصيانة، فإنها تحمي نفسها ماليًا بينما تبني علاقات أقوى مع العملاء الذين يقدرون معرفة أن معلوماتهم الحساسة تظل آمنة بعيدًا عن أعين المتطفلين.
تدريب الموظفين على الصيد الإلكتروني وتعامل البيانات
إن تدريب الموظفين بانتظام حول عمليات الاحتيال عبر البريد الإلكتروني (Phishing) وممارسات التعامل مع البيانات بشكل صحيح يُحدث فرقاً كبيراً في الحفاظ على أمان أنظمة نقاط البيع. وبحسب مختلف الدراسات، فإن حوالي 80 بالمئة من جميع تسريبات البيانات تحدث بسبب عدم معرفة الموظفين بما يجب عليهم فعله، أو بسبب إهمالهم لبروتوكولات الأمان الأساسية. ولذلك يُعد التدريب المستمر أمراً بالغ الأهمية. فعندما تُنظم الشركات جلسات تدريبية تُحاكي هجمات الاحتيال الإلكترونية الحقيقية، يحصل الموظفون على خبرة عملية في اكتشاف رسائل البريد الإلكتروني المشبوهة وكيفية الرد بشكل صحيح دون الذعر. والنتيجة الإيجابية؟ يصبح الموظفون أكثر كفاءة في حماية المعلومات السرية، مما يقلل من احتمالية حدوث اختراقات. ودعونا نواجه الأمر، لا يرغب أحد في أن تُسرق تفاصيل عملائه الشخصية أو أن تتعرض سمعة شركته للضرر بسبب حادث سيبراني كان يمكن تجنبه.
المنتجات الموصى بها
أخبار ساخنة
-
بطاقة ذكية 2019
2024-01-23
-
ترستيك 2019
2024-01-12
-
فيوتيركوم 2019
2024-01-12
-
المدفوعات السلسة آسيا 2020
2024-01-12
-
الشرق الأوسط السلس 2022
2024-01-12

 EN
EN
 AR
AR
 BG
BG
 CS
CS
 DA
DA
 NL
NL
 FR
FR
 IT
IT
 JA
JA
 KO
KO
 PL
PL
 PT
PT
 RU
RU
 ES
ES
 TL
TL
 ID
ID
 LT
LT
 UK
UK
 VI
VI
 HU
HU
 MT
MT
 TH
TH
 TR
TR
 FA
FA
 AF
AF
 MS
MS
 MK
MK
 HY
HY
 AZ
AZ
 KA
KA
 BN
BN
 BS
BS
 LO
LO
 MN
MN
 NE
NE
 ZU
ZU
 MY
MY
 KK
KK
 UZ
UZ
 KY
KY